The T-Mobile Sidekick 4G has only been on sale since Wednesday, but that hasn’t slowed down the rooting masters at xda-developers. They’ve already come up with a root for the messaging-centric smartphone, opening the door to custom ROMs and other juicy hacks.
The root is the handiwork of “josby”, but according to other xda members there are several ways to hack the Sidekick 4G. Next up is stripping away some of the preinstalled apps T-Mobile load onto the handset, which may give it an extra turn of speed.
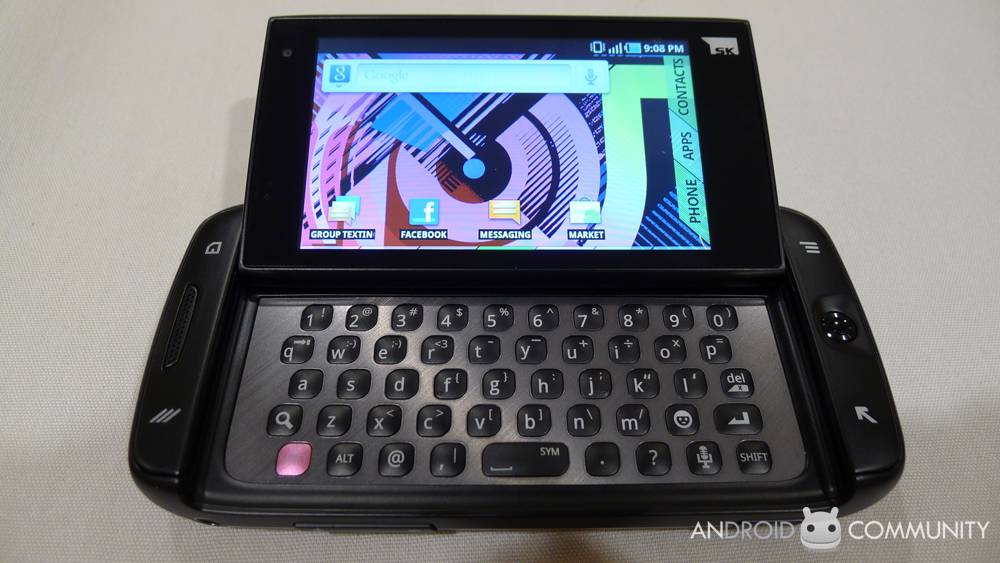
We found the Sidekick to be something of a unique proposition among Android devices, doing a darn good job of following in the footsteps of its unusual predecessors and differentiating itself for a pretty specific market. More on the Sidekick 4G in the full Android Community review.
[Thanks Kenny!]
1) enable debug USB mode on your phone
2) install Samsung drivers for the phone – right now Samsung’s site seems to not have a choice for the Sidekick 4G’s model (SGH-T839), but I grabbed the drivers for the Vibrant (at www .samsung.com/us/support/downloads/SGH-T959ZKDTMB) and they worked.
3) get adb shell working on your PC (Google it)
4) download the rageagainstthecage-arm5.bin and Superuser packages from the links in this page: wiki.cyanogenmod.com/index.php?title=HTC_Hero_%28CDMA%29:_Full_Update_G uide (be sure to unzip the files into the directory where your adb.exe program is unless you’ve put it in your path)
5) reboot your phone and plug it in
6) adb push rageagainstthecage-arm5.bin /data/local/tmp
7) adb shell
8) cd /data/local/tmp
9) chmod 755 rageagainstthecage-arm5.bin
10) ./rageagainstthecage-arm5.bin
11) wait until you get booted back out to your DOS command prompt
12) adb kill-server
13) adb start-server
14) adb shell
15) you should now be at a # prompt. The first few times I tried, I wasn’t – I was at $. Doing this from a fresh boot seemed to be the trick. Reboot your phone and try again if you’re getting a $.
16) mount -o remount,rw /dev/block/stl9 /system
17) exit
18) adb push su /system/xbin
19) adb shell chmod 4755 /system/xbin/su
20) adb push Superuser.apk /system/app
21) adb shell mount -o remount,ro /dev/block/stl9 /system
22) exit
23) reboot the phone then run an app that requests root, such as Root Explorer, to verify










Seems complicated is there just an appp that will do it like easy root
The T839 model is now available, but there are two “model codes” to choose from…can’t find a similar code in the About section of my Sidekick… :-/