Yesterday, we reported that bloggers had found a vulnerability in the Skype App which allows hackers to harvest data from a user’s Android handset with no need to root a phone or gain special permission. The problem was discovered during the testing of a leaked version of Skype for Android’s new Video App. But it didn’t take long to notice that the flaw was carried over from the already released Skype for Android App that’s currently in the Market. Skype has responded to the news in their security blog, admitting that the flaw exists and they’re working hard to fix it. But what can a user do to protect themselves in the meantime?
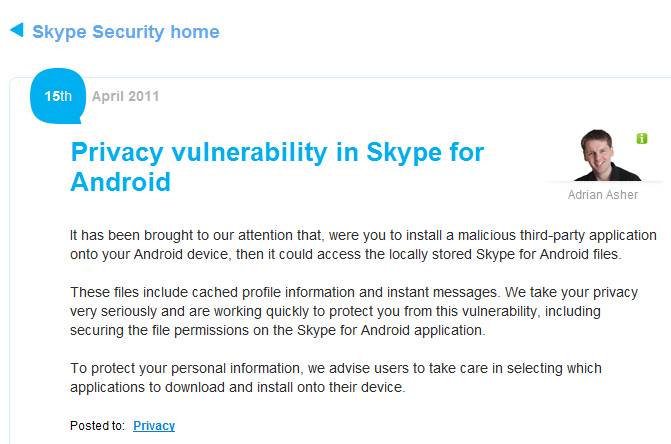
We take your privacy very seriously and are working quickly to protect you from this vulnerability, including securing the file permissions on the Skype for Android application,” said Andrian Asher on the Skype Security blog.
Skype has been downloaded by over 10 million Android users, so the impact of this news was pretty severe. Skype recommends a rather weak solution … don’t download the app. In other words … “Doctor, it hurts when I do this … Doctor: well don’t do that.” But really, what else can Skype do until they fix the problem and release a new app?
It also underscores a flaw in the entire system … how can you tell what apps are vulnerable what apps aren’t? One thing that users can do to protect themselves is to look at what permissions an app requires. That information will just before you hit “install.” If you don’t think the app needs all that data, then you should not install it.
[via PCWorld]









