
Pokemon GO is not even on global launch yet, and it’s already causing quite a stir in the world. Where the game is available, users are already burning the miles on their shoes and bikes, walking around communities and neighborhoods to catch ‘em all. The excitement in social media is quite palpable, and so we understand the envy of those who reside in territories where the app hasn’t launched yet. There are people there who have resorted to side-loading illegal APKs. The dangerous thing here is that there’s a modified APK going around that does more harm to you than just bring you a good game.
Proofpoint, a security research outfit, has the goods on an infected Pokemon GO APK installer that unfortunately also contains a malicious remote access tool (RAT) called Droidjack (also known as SandroRAT) that when enabled on your devices will give hackers the ability to take full control over a victim’s phone. That means the attacker will have control and access to your data, personal files, contacts, messages, and apps.
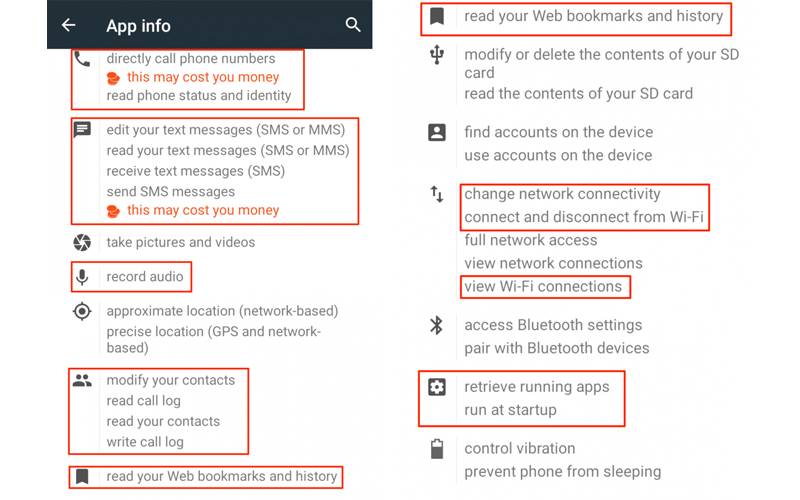
There are two ways you can check whether your APK is ok. First is through the SHA256 hash, a specific code that verifies if a file is the same as the original — the legit app often linked to by proper media outlets has a hash of 8bf2b0865bef06906cd854492dece202482c04ce9c5e881e02d2b6235661ab67. The malicious APK that was analyzed has a SHA256 hash of 15db22fd7d961f4d4bd96052024d353b3ff4bd135835d2644d94d74c925af3c4. Also, you can check the permissions that the app asks for and see the image below, a sample of what the infected app’s permissions are.
The best way to protect yourself? Stop this side-loading madness and wait for the official launch of the game in your territory. I know it’s easy for us to say, the game is already out in the US. But rather than open yourself up to malicious attacks, waiting is such a better option.
SOURCE: Proofpoint









