Android security has sometimes become the butt of jokes in the mobile market. Despite Google’s best machine learning systems, malware-bearing apps still get through to users, often from unverified, unofficial, and third-party sources. This has made Android phones non-ideal for users at risk from targeted attacks, like journalists and activists. That is why, starting today, Android will no longer allow apps to be installed outside of the Google Play Store on devices enrolled in Google’s Advanced Protection program.
To be clear, Google isn’t taking the ability to sideload APKs across all of Android. This new policy only applies to Android devices that are part of its high-security program for high-risk users. The rest of the Android world can continue installing apps left and right at their own risk. That is until Google decides to put its foot down there as well.
There are some exceptions even for Advanced Protection devices. Pre-installed apps and those that OEMs provide via their own stores can still be installed and those that were already sideloaded before this day will continue to work. More advanced users can also still sideload apps via ADB if they know how. Unfortunately, that may also mean that anyone that has physical access to the user’s phone can as well.
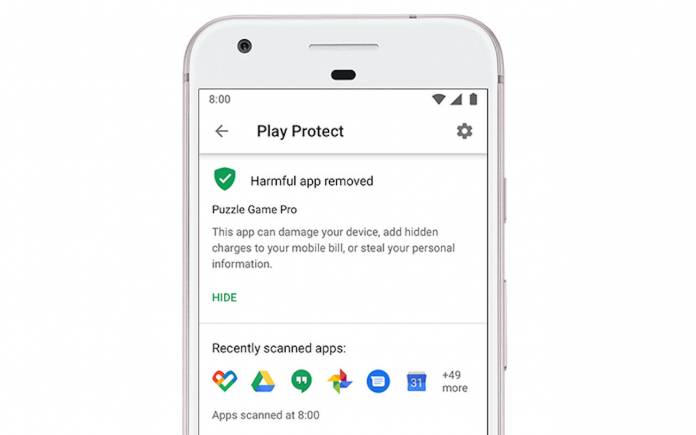
Google is also turning on Play Protect on these devices by default, which is surprising it took this long to implement. Play Protect routinely scans apps installed on phones to check for malware or unauthorized changes.
All these protections revolve and rely on Google Play Store and services being installed, which is, of course, a way for Google to indirectly advertise and increase reliance on its proprietary framework. That said, some will readily point out how often malicious apps are able to bypass Google Play Store’s defenses, making those protections moot.









