4G connectivity for our smartphones – the formal standard more commonly known by the specific name LTE – is so pervasive and ubiquitous that we just take it for granted these days. Most modern smartphones need to have LTE connectivity to keep up with the times, but we never ask the question if our network activity over LTE is secure. Research now shows that our connection to a mobile network over LTE is not that secure.
Researchers have found vulnerabilities in the formal standards of LTE, which make users vulnerable to potential attacks. These vulnerabilities have been discovered and the details have now been published by David Rupprecht, Katharina Kohls, Thorsten Holz, and Christina Pöpper of Ruhr-Universität Bochum and New York University Abu Dhabi. There are three types of attacks that can be done over an LTE connection. Two of these attacks are passive, allowing hackers to listen to network traffic and attempt to steal private information. The third is an active attack which the researchers call “aLTEr.”
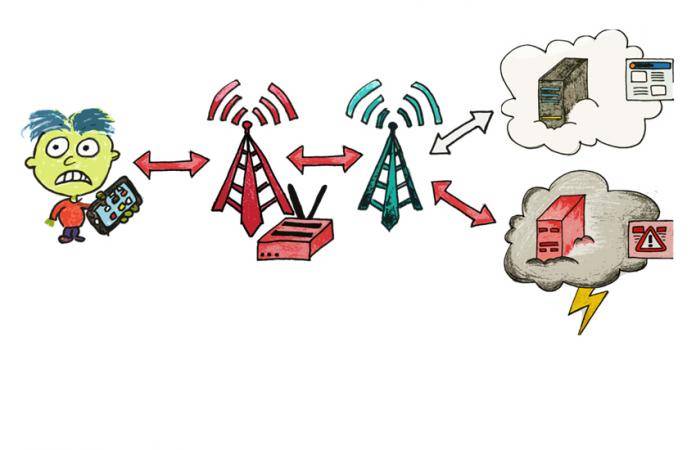
The attacks include determining user identities in a radio cell, getting website browsing information, and actively altering DNS traffic to hijack a given connection and redirect victims to malicious sites. In the defense of the users, an aLTEr attack is very complex and needs a lot of things to happen to pull off successfully. Such an attack relies heavily on outside infrastructure – a DNS redirect, only possible because of inconsistent application of authentication across LTE layers.
According to the research:
LTE uses mutual authentication on the layers above the data link layer to prevent Bob’s phone from connecting to a fake network. However, the layers below are unprotected and an attacker can forward high-layer messages. Bob’s phone still assumes that he is connected to the original network. For the user data redirection attack, we exploit that the user data is not integrity protected. Thus an attacker can modify the content of a packet if she knows the original plain text, even the packet is encrypted. In the case of DNS packets, we know the destination address of the original DNS server. For the redirection, the attacker adds a specific offset, thus the DNS request is redirected to a DNS server under the adversary’s control.

Doing an aLTEr attack requires hackers to have a malicious DNS server, as well as a phishing website in place to harvest the credentials of users who are redirected to that site via their phone’s browser. On top of that, the hackers will need an extensive amount of hardware. Also, hackers need to be reasonably close (up to 2km) to the target to even be able to do this.
But the bottom line is that the hack can be done, as these researchers have now proven. The researchers have notified the GSM Association (GSMA) of their findings earlier this year, and they in turn informed network providers and the 3rd Generation Partnership Project (3GPP), which is the specification body responsible for the development and maintenance of LTE, related 4G standards, and 5G standards.
SOURCE: aLTEr Attacks









