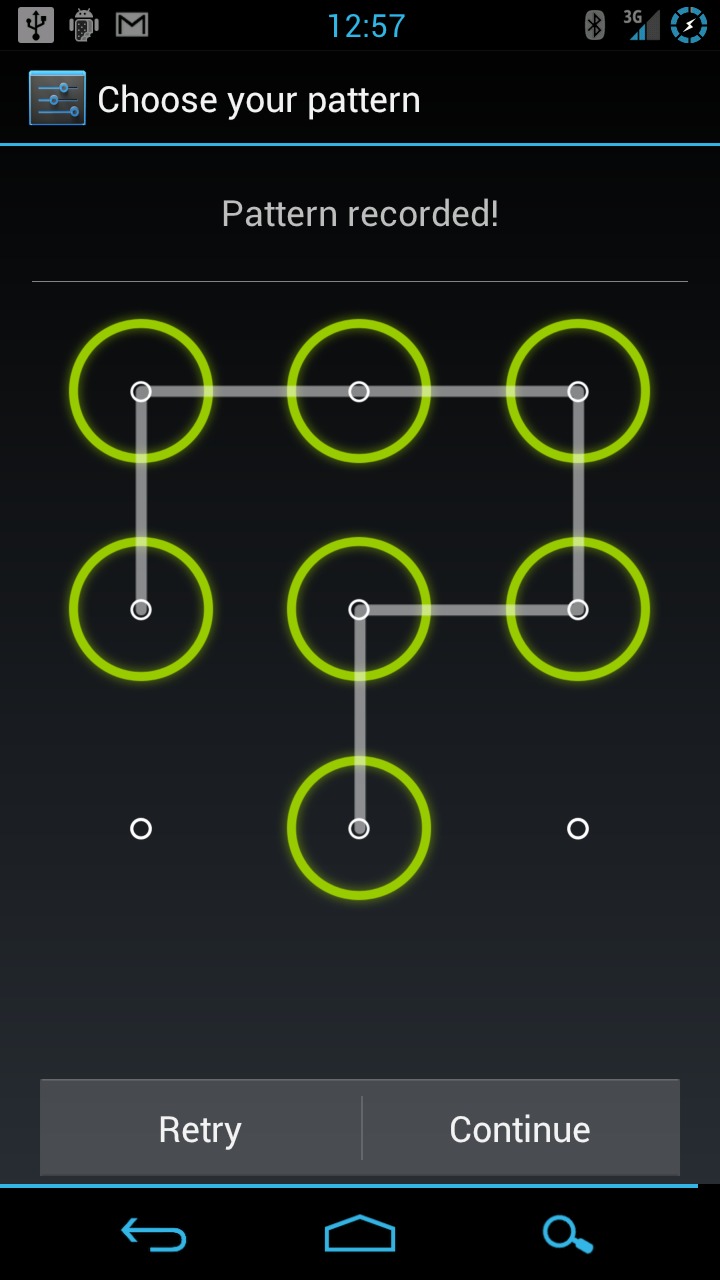
There have been a lot of stories in the last few months questioning Android’s security as a platform. But when it came time for FBI investigators to look through an accused pimp’s Android phone, they were rendered helpless by the pattern lock that’s been part of the OS for years. After failing to break into the phone itself, they’ve submitted a subpoena to Google for the suspect’s username and password, in order to make their case in federal court.
It’s important to note that the investigators have a warrant for the data on suspect Dante Dears’ phone, even though they don’t technically need one. (In many jurisdictions, arresting authorities can make a cursory examination of your cell phone or computer if they’re on your person when arrested. Breaking through PINs, passwords or other security usually necessitates a warrant.) Apparently the FBI tried the good old-fashioned guessing game enough times to lock down the phone (20 unsuccessful patterns), and now require Google’s help to get access to Dears’ data. Dears isn’t cooperating, and Google hasn’t responded to the subpoena yet.
The FBI is after quite a lot of data, including some that Google may not have. In addition to the account email and password, they’re hoping for a Social Security number (don’t they already know that?), a contact list, all email accounts accessed from the phone, every web page visited with time and duration, all search terms and GPS logs, and “Verbal and/or written instructions for overriding the ‘pattern lock’ installed on the phone”. Despite the fact that Google doesn’t necessarily log all that information, it may not hold up in court, either; the FBI is likely “fishing” for any and all information they might be able to use to further their case.
Android Community wishes to make it clear that we don’t support Dante Dears or his actions. The FBI has a warrant for the information, so more power to them. But if you’ve got something you son’t want others to see, it looks like Android’s pattern lock is a good way to make sure they don’t.
[via Ars Technica]










“Verbal and/or written instructions for overriding the ‘pattern lock’ installed on the phone”. I am in no way condoning the actions of the accused but view this as an attempt to gain access to all Android devices. I was ok with all their requests but this one. If Google gives this out it will destroy the purpose of the pattern lock. I believe that given this information the FBI will then be able to use it on any android with out warrant. This is like asking a safe company for a master combo. It would put the safe company out of business if it gave out or included a master combo.
99.9% of cryptographic software has built-in backdoors that are accessible to the US government. Most encryption requires this by law.
Which is the reason to use open sourced ones such as TrueCrypt.
American law maybe, not all countries are basically being run by a score of giant secret service organizations
If you try an Android lock and fail too many times, Android will prompt for the Google password and override the lock. So Google can get in by changing the account password.
Just remember to keep the phone clean, and it works great. But the pattern can be visible if you use your phone with greasy fingers (and don’t clean it) or if your phone has a fingerprint problem (most don’t anymore unless something happens to the coating on the glass or plastic).
Well after I unlock the screen, I tend to move around and use the phone enough before putting it away again that the pattern is practically gone.
I know it is usually fine, though it is best to make sure the unlock pattern cannot be seen on your phone after entering it. Especially if your just sending a quick message or something and not using the screen much since it wouldn’t get smudged over. Otherwise it is far more secure than a typical password.
Oh Google could use a multilevel lock system. Meaning you show your face to the camera while entering a password be it the normal pin number one of this one or both
My droid can’t do that, it doesn’t have a front camera. And do you know if it can be tricked by a photo of your face? I know some systems that can’t see if the object is three dimensional or not or any other method to see detect if it’s just a picture and not a person. I love the idea and I am sure it would work great in a combination with the pattern lock though. Did anyone test this? I haven’t heard of it being a problem, but I still don’t know if it can be tricked.
Hey, we found a simple way to gain unlimited attempts at gesture unlocking an Android phone and shot a video walk-though. If the FBI had done this, they would not have to have subpoenaed Google for the phone owner’s credentials. Here’s our write-up: http://blog.deepthoughtlab.com/2012/03/how-to-gain-unlimited-android-gesture.html